
Can you go back to 2013? The novelty of social media apps, implementing VPN policies for home working, and driverless cars were a new concept (still). So, what's changed in the last 10 years? ..the world!
We've moved from watching science fiction on cinema screens to real time science fiction augmentation experiences, integrated technologies that transcend from first line interactions to predictive technologies across the entire ecosystems being embedded into Industry 4.0 supply chains. Fortunately, our ears have not turned into Wi-Fi aerials, but that could be changing too as cybernetic-implants advance.
In 2013, my MBA researched the ‘management of cyber security’ which included the topic of cyber insurance and suggested that most industries, including finance and health technology were far away from ‘codifying business and technical transactions’ and at best, if the risks were quantified, risk appetites were understood and insured against i.e., taking a risk transfer approach.
In their report, titled "UK Cyber Insurance H1 2022 Trends' [1] Marsh Speciality reported that 'Cyber insurance pricing again increased in the first two quarters, while the level of underwriter scrutiny of cyber controls persisted'. Their report acknowledges that when it comes to insurance claims, data will always lag, but over recent years, the actual quality of data required to perform claims validation continues to develop. This is good, as it continues to highlight for all organisations what cyber hygiene mechanisms they should have in place and what data is present due to those cyber hygiene mechanisms, specifically, if they are sufficient to validate a claim, or be branded as negligent, making sure and safeguarding any data disclosures without penalty implications.
According to the Cyber Security Breaches Survey 2023 conducted by the UK government [2], under four in ten businesses (37%) and a third of charities (33%) report being insured against cyber security risks. This figure rises to 63% of medium businesses and 55% of large businesses, meaning that cyber insurance is more common in medium businesses than large ones.
IASME who are NCSCs delivery partner for the UK’s Cyber Essentials programme [3] ensure their certifications have the basics in place, but even the basics can be costly, so whilst smaller organisations look at the ability of each technology implemented to provide the granular security controls to meet IASME’s Cyber Essentials, larger organisations can afford to have enterprise teams in place to meet the Cyber Essentials requirements, however to have no cyber security presence, and knowing that most industries are now completing their digital transformation efforts (that identified and modernised legacy debt) by taking advantage of codifying laas, Paas and Saas solutions, would allow yourself to be seen as 'not making an effort' to secure your business activities, this is why the modern Cyber Essentials certification, if eligible, provides free Cyber Insurance.
As highlighted in figure 1, my MBA research identified that information asymmetry between customers and providers was the reason for the overpricing in cyber insurance products, however to help the lack-lustre of insurance, insurance firms used contracted deductibles of vendor-sla's with a contract-pricing approach that moved the balance back to information asymmetry so appearing to provide value-add-services to reduce the overall contract cost.
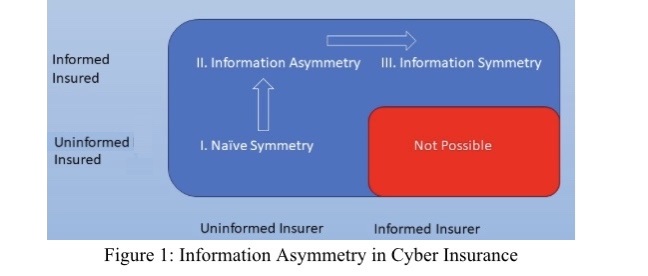
Figure 1: Information Asymmetry in Cyber Insurance
Fast forward 10 years, in the Marsh Speciality report, they found that "in the first half of 2022, more than 90% of clients experienced cyber insurance pricing increases as per figure 2 below. The two primary levers available to insureds to combat price increases and maintain budget are to decrease limits and increase retentions. In many cases, the increases in retentions have been driven more by insurers than buyers as shown in figure 3, as insurers want insureds to have more 'skin in the game', which has driven up the average retentions".

What does this mean?
It certainly does not mean gamification of the cyber insurance markets, where better appropriate and proportionate controls, such as multi factor authentication, email scanning, network segmentation, taking regular backups, privilege access controls or basic malware checking, and effective risk profiling means you get better premiums, but it does mean, well known concepts like 'security by design' and 'zero trust models' will be cited ‘more and often’ which will help with overall cyber thematic across all industries, this therefore will have a trickle down effect into legacy and emerging technologies, from blockchain industries to health technologies. These concepts in turn promote better cyber awareness on what specifics an organisation needs to have in place when dealing with regulatory bodies like the UK’s Information Commissioner's Office.
Outside of the UK, the European Commission has proposed the EU Cyber Solidarity Act [4], to improve the response to cyber threats across the EU. The proposal will include a European Cybersecurity Shield and a comprehensive Cyber Emergency Mechanism to create a better cyber defence method. It covers connected objects in the home, hospitals, energy grids and railways, with focus on Cross-border Security Operations Centres to procure cyber threat detection tools and services - again, this highlights the need for optimised security controls and monitoring of them.
In April 2023, NCSC updated its Toolkit [5], for boards to ensure that cyber resilience and risk management are embedded throughout their organisations, these toolkits encourage boards to have cyber conversations on how they are prepared, or even how using existing data can help them remain cyber ready against the most dangerous ransomware out in the wild. Along with providing guidance for cyber insurance [6] within the UK, they have also sponsored an independent study [7], which amongst others, makes the case for ‘interventions that would improve UK market-wide ransom discipline so that fewer victims pay ransoms, or pay lower demands’ to help balance out any assumptions that 'ransomware operators are deliberately targeting organisations with insurance’.
Summary
In summary, you do not want to be the organisation or leadership team who has just found out they've been hacked by being on the news, and given that digitalisation for businesses is now normal where you want to give the best competitive customised technology solutions to your clients at the cheapest possible cost, would not mean you need to compromise security postures. Instead, your teams, whether that be operations, red, yellow, blue or purple teams, should be familiar with good cyber practices, such as 'Secure System Architecture and Design' principles found at the Council's career framework [8].
This will make sure you know why you have certain security controls in place and why they have been configured the way they have. So, when it comes to demonstrating your insurance claim validations, you not only have the confidence of explaining that best practices are embedded, but you also have staff that can explain your technologies and polices against security postures effectively because they have been constantly developing their competencies by being professionally registered with the Council [9]. By subscribing to the Council's professional standards [10] staff are well on their way to being Chartered Cyber Security Professionals. Overall, this ensures you maximise your investments in cyber technology as your skilled staff will keep your cyber security posture intact for decades to come (and keep cyber insurance premiums down).
#RUCyberReady
References:
[1] https://www.marsh.com/uk/services/cyber-risk/insights/uk-cyber-insurance-trends-report-h1-2022.html
[2] Cyber security breaches survey 2023 - GOV.UK (www.gov.uk)
[3] https://iasme.co.uk/cyber-essentials/
[4] https://digital-strategy.ec.europa.eu/en/policies/cyber-solidarity
[5] https://www.ncsc.gov.uk/collection/board-toolkit
[6] https://www.ncsc.gov.uk/guidance/cyber-insurance-guidance
[9] https://www.ukcybersecuritycouncil.org.uk/professional-standards/professional-registration-roadmap/
[10] https://www.ukcybersecuritycouncil.org.uk/professional-standards/
Figures:
Figure 1: Adapted from Figure 8. Tridib Bandyopadhyay, Vijay S. Mookerjee, Ram C. Rao, Communications of the ACM, Vol. 52 No. 11, Pages 68-73, 10.1145/1592761.1592780
Figure 2: Adapted from Figure 3. Page 6 https://www.marsh.com/uk/services/cyber-risk/insights/uk-cyber-insurance-trends-report-h1-2022.html
Figure 3: Adapted from Figure 4. Page 6 https://www.marsh.com/uk/services/cyber-risk/insights/uk-cyber-insurance-trends-report-h1-2022.html
